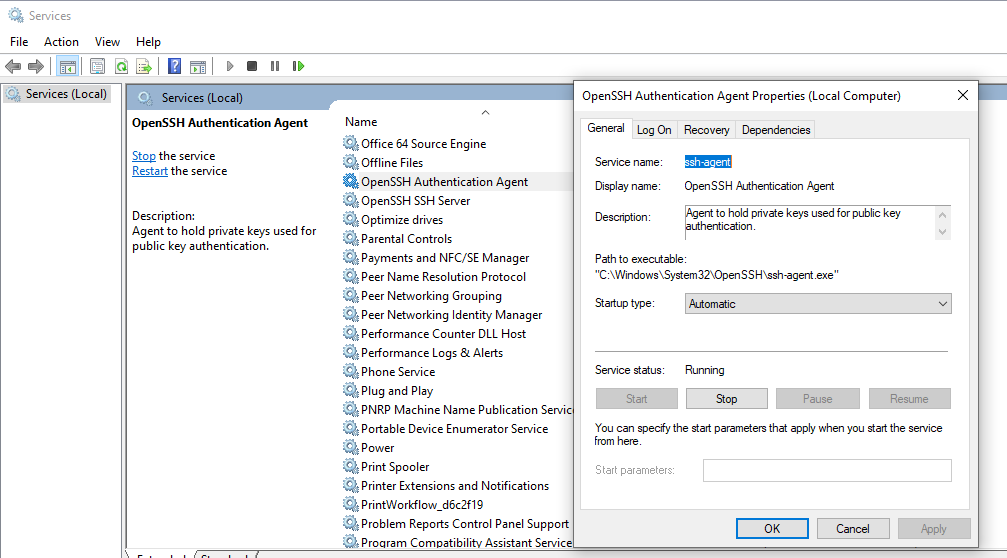
You must configure OpenSSH Authentication Agent service to automatically start (or you can start it manually everytime when opening your powershell for the first time: Start-Service ssh-agent). After that, you need to ssh-add C: path to your ssh key idrsa only once. After that, everytime the ssh-agent is started, the key will be there. Ssh-agent.exe file information Ssh-agent.exe process in Windows Task Manager. The process known as OpenSSH Authentication Agent appears to belong to software OpenSSH for Windows or Git by unknown. Description: Ssh-agent.exe is not essential for the Windows OS and causes relatively few problems. The ssh-agent.exe file is located in a subfolder of the user's profile folder (mostly C:Users.
-->Most authentication in Windows environments is done with a username-password pair.This works well for systems that share a common domain.When working across domains, such as between on-premise and cloud-hosted systems, it becomes vulnerable to brute force intrusions.
By comparison, Linux environments commonly use public-key/private-key pairs to drive authentication which doesn't require the use of guessable passwords.OpenSSH includes tools to help support this, specifically:
- ssh-keygen for generating secure keys
- ssh-agent and ssh-add for securely storing private keys
- scp and sftp to securely copy public key files during initial use of a server
This document provides an overview of how to use these tools on Windows to begin using key authentication with SSH.If you are unfamiliar with SSH key management, we strongly recommend you review NIST document IR 7966 titled 'Security of Interactive and Automated Access Management Using Secure Shell (SSH).'
About key pairs
Key pairs refer to the public and private key files that are used by certain authentication protocols.
SSH public-key authentication uses asymmetric cryptographic algorithms to generate two key files – one 'private' and the other 'public'. The private key files are the equivalent of a password, and should stay protected under all circumstances. If someone acquires your private key, they can log in as you to any SSH server you have access to. The public key is what is placed on the SSH server, and may be shared without compromising the private key.
When using key authentication with an SSH server, the SSH server and client compare the public keys for username provided against the private key. If the server-side public key cannot be validated against the client-side private key, authentication fails.
Multi-factor authentication may be implemented with key pairs by requiring that a passphrase be supplied when the key pair is generated (see key generation below).During authentication the user is prompted for the passphrase, which is used along with the presence of the private key on the SSH client to authenticate the user.
Host key generation
Public keys have specific ACL requirements that, on Windows, equate to only allowing access to administrators and System.To make this easier,
- The OpenSSHUtils PowerShell module has been created to set the key ACLs properly, and should be installed on the server
- On first use of sshd, the key pair for the host will be automatically generated. If ssh-agent is running, the keys will be automatically added to the local store.
To make key authentication easy with an SSH server, run the following commands from an elevated PowerShell prompt:
Since there is no user associated with the sshd service, the host keys are stored under ProgramDatassh.
User key generation
To use key-based authentication, you first need to generate some public/private key pairs for your client.From PowerShell or cmd, use ssh-keygen to generate some key files.
This should display something like the following (where 'username' is replaced by your user name)
You can hit Enter to accept the default, or specify a path where you'd like your keys to be generated.At this point, you'll be prompted to use a passphrase to encrypt your private key files.The passphrase works with the key file to provide 2-factor authentication.For this example, we are leaving the passphrase empty.
Now you have a public/private ED25519 key pair(the .pub files are public keys and the rest are private keys):
Remember that private key files are the equivalent of a password should be protected the same way you protect your password.To help with that, use ssh-agent to securely store the private keys within a Windows security context, associated with your Windows login.To do that, start the ssh-agent service as Administrator and use ssh-add to store the private key.
After completing these steps, whenever a private key is needed for authentication from this client, ssh-agent will automatically retrieve the local private key and pass it to your SSH client.
Note
It is strongly recommended that you back up your private key to a secure location,then delete it from the local system, after adding it to ssh-agent.The private key cannot be retrieved from the agent.If you lose access to the private key, you would have to create a new key pairand update the public key on all systems you interact with.
Deploying the public key
To use the user key that was created above, the public key needs to be placed on the server into a text file called authorized_keys under usersusername.ssh.The OpenSSH tools include scp, which is a secure file-transfer utility, to help with this.
To move the contents of your public key (~.sshid_ed25519.pub) into a text file called authorized_keys in ~.ssh on your server/host.
This example uses the Repair-AuthorizedKeyPermissions function in the OpenSSHUtils module which was previously installed on the host in the instructions above.
These steps complete the configuration required to use key-based authentication with SSH on Windows.After this, the user can connect to the sshd host from any client that has the private key.
Summary
The integration of SSH has been a popular request among Windows users and SSH presents a renewed vision for remoting. Microsoft’s goal is to tightly integrate the open source Secure Shell (SSH) protocol with Windows and PowerShell. As a result, admins now have two-way remote management with PowerShell and SSH, from Linux to Windows and vice versa. We will also see that system administrators will be able to manage Linux servers, routers, switches, and other devices that allow for SSH. Realizing this vision is important as it allows traditional Windows and Linux admins to manage any operating system with a common skill set plus allowing for cross-platform code and scripts. What’s more, we see that configuration automation through Azure DSC can be leveraged for both Windows and Linux operating systems. Depending on the task, we can run the exact same PowerShell Core code on all platforms. Presently, there are caveats, limitations and the technology is continuing to evolve so keeping up to date is necessary. What this means for managing Office 365 in the future is also a question this author would like to know. Though, OpenSSH has arrived to the Windows OS after many years in development, and it’s still a work in progress as Microsoft’s PowerShell team is contributing to the development efforts of the open source OpenSSH community. This article will provide a step by step procedure for installing & configuring the new OpenSSH Server and client and also provide an explanation of the PowerShell remoting architecture as context. The article will cover remoting scenarios and steps however a walk-through for configuring Linux will not be part of this article.
Problem
- Microsoft is transitioning to “PowerShell Core” and cross-OS compatibility, while moving away from “Windows PowerShell”. Microsoft recently explained its “Windows PowerShell” roadmap plans, which will focus on “PowerShell Core”, going forward.
- There are now two editions of PowerShell called “Windows PowerShell” & “PowerShell Core”. However, there are no plans to introduce new functionality to “Windows PowerShell”.
- PowerShell remoting normally uses WinRM for connection negotiation and data transport, which is not supported in .NET Core so SSH was chosen for remoting since it allows true multi-platform remoting.
- Admins will be required to learn new remoting commands, use-cases and will need to update scripts.
- OpenSSH has to be installed and configured manually on both the server and client.
- Based on the various articles, there are a couple different ways to get SSH installed and configured on Windows OS.
- The install and configuration process can be a bit involved and has proven to be difficult for some administrators.
- Updated New-PSSession, Enter-PSSession and Invoke-Command cmdlets now have a new parameter set to facilitate the new remoting connections. Evolving cmdlets means admins must understand the differences and update their scripts at some point.
PowerShell Remoting Architecture
OpenSSH is a freely available collection of client/server utilities that enable secure remote login, remote file transfer, and public/private key pair management. As part of the OpenBSD project, the Secure Shell (SSH) protocol family of tools were developed and has been used for many years across the BSD, Linux, macOS, and Unix ecosystems. Back in 2015, the Microsoft PowerShell team announced support and commitment to the OpenSSH community and code base. This commitment resulted in direction and architectural changes for PowerShell.
Microsoft’s solution for PowerShell remoting was Windows Remote Management (WinRM) which handles remote connection negotiation and data transport by means of the WS-Management Protocol, which is based on SOAP (Simple Object Access Protocol). WinRM is an implementation of the Web Services for Management (WS-Man) specification, which takes advantage of firewall-friendly HTTP (TCP port 5985) or HTTPS (TCP port 5986) protocols to establish the communications channel.
Although Windows PowerShell users are used to WinRM as their remoting protocol with PowerShell, both customers and internal Microsoft product teams wanted to enable Windows to use SSH. The ability to use SSH provides a common user experience for Linux users to connect to Windows systems remotely and vice versa. SSH will likely become the remoting protocol of choice for Windows users and as part of the future direction of all Microsoft applications.
Given Microsoft’s new cross platform vision, the WinRM service is now considered limited by being Windows-specific. WinRM is not yet available as part of multi-platform PowerShell Core therefore, SSH was chosen for the remoting implementation since it is now available for both Linux and Windows platforms and allows multi-platform PowerShell remoting. Of note, the PowerShell team has configured the Linux PowerShell engine to do WS-Man remoting. Linux supports WS-Man remoting through PowerShell Remoting Protocol (MS-PSRP) and with the Open Management Infrastructure (OMI) provider. Installation of both OMI and the OMI provider on Linux is required for PowerShell remoting. Currently, PowerShell Core supports PowerShell Remoting (PSRP) over WSMan with Basic authentication on macOS and Linux, and with NTLM-based authentication on Linux. (Kerberos-based authentication is not supported.)
PuTTY on Windows is the most common SSH client utility, as it allows a Windows user to SSH into a Linux system. There are other third-party SSH server solutions for Windows, however an integrated Microsoft solution will allow for further application integration, extended functionality and support.
Installing OpenSSH
Installing OpenSSH package Option 1) Manually from Github
- Download the latest build of OpenSSH from a web browser.
- Otherwise, download the latest build in an elevated PowerShell console, run the following:
Invoke-WebRequest https://github.com/PowerShell/Win32-OpenSSH/releases/download/v1.0.0.0/OpenSSH-Win64.zip -OutFile openssh.zip
- Extract contents of the latest build to
C:Program FilesOpenSSH - Otherwise, you can extract the zip file in an elevated Powershell console, run the following:
Expand-Archive .openssh.zip 'C:Program Files'- Verify the sub-directory name, as the command will create “OpenSSH-Win64”
- Launch PowerShell as an Administrator and go to the directory where the files have been extracted to:
cd 'c:Program FilesOpenSSH'
- In an elevated PowerShell console, run the following
powershell.exe -ExecutionPolicy Bypass -File install-sshd.ps1
- Open the firewall for sshd.exe to allow inbound SSH connections
New-NetFirewallRule -Name sshd -DisplayName 'OpenSSH Server (sshd)' -Enabled True -Direction Inbound -Protocol TCP -Action Allow -LocalPort 22
- If you are running these commands on Windows 10, run the command
netsh advfirewall firewall add rule name=sshd dir=in action=allow protocol=TCP localport=sshd
- Start the windows service sshd (this will automatically generate host keys under %programdata%ssh if they don’t already exist)
- Run the command: Start-Service sshd
- Migrate sshd configuration:
- To use existing customized sshd_config, you need to copy it from binary location to %programdata%sshsshd_config (Note that %programdata% is a hidden directory).
- To use existing host keys, you need to copy them from binary location to %programdata%ssh
- Prior versions required SSHD resources (sshd_config, host keys and authorized_keys) to have READ access to “NT ServiceSSHD”. This is no longer a requirement and the corresponding ACL entry should be removed. Run
Powershell.exe -ExecutionPolicy Bypass -Command '. .FixHostFilePermissions.ps1 -Confirm:$false'(Note the first “.” is a call operator.) to fix up these permissions.
- Change the services
sshdandssh-agentto auto-startSet-Service sshd -StartupType AutomaticSet-Service ssh-agent -StartupType Automatic
- Verify the change in the GUI and check for the services sshd & ssh-agent with: services.msc
- Configure the default ssh shell by running regedit.exe
- On the server, configure the default ssh shell in the windows registry by navigating to the key: ComputerHKEY_LOCAL_MACHINESOFTWAREOpenSSH
- Create a key called “DefaultShell” of type “REG_SZ”
- Enter the string value as “C:windowssystem32WindowsPowerShellv1.0powershell.exe”
- If PowerShell core is installed, then the string value will be “c:Program FilesPowerShell6.0.1pwsh.exe” (assuming version 6.0.1 however verify your installed version.)
Installing OpenSSH package Option 2) using PowerShell
Name : OpenSSH.Client~~~~0.0.1.0
State : NotPresent
Name : OpenSSH.Server~~~~0.0.1.0
State : NotPresent
Add-WindowsCapability -Online -Name OpenSSH.Client~~~~0.0.1.0
Add-WindowsCapability -Online -Name OpenSSH.Server~~~~0.0.1.0
Path :
Online : True
RestartNeeded : False
Installing the OpenSSH package Option 3) using Chocolatey
- There are multiple ways to install OpenSSH on Windows. Chocolatey automates a few of the tasks.
- Open PowerShell command prompt (or cmd.exe) as Administrator
- If Chocolatey is not installed, follow the steps documented on the chocolatey.org site
- Run the command: choco install openssh -params ‘”/SSHServerFeature /KeyBasedAuthenticationFeature”‘ –y
Installing OpenSSH package Option 4) using DISM.exe
Capability Identity : OpenSSH.Client~~~~0.0.1.0
Capability Identity : OpenSSH.Server~~~~0.0.1.0
dism /Online /Add-Capability /CapabilityName:OpenSSH.Client~~~~0.0.1.0
dism /Online /Add-Capability /CapabilityName:OpenSSH.Server~~~~0.0.1.0
Installing OpenSSH package Option 5) using Windows Developer Mode
Windows Develop Mode is not Microsoft’s OpenSSH implementation. Do not install SSH this way. SSH services are enabled when you enable Device Discovery on your device. This is used when your device is a remote deployment target for UWP applications. The names of the services are ‘SSH Server Broker’ and ‘SSH Server Proxy’. The existing SSH server used in Windows Developer Mode is not yet protocol compliant.
Installing OpenSSH package Option 6) using Enable-SSHRemoting PowerShell Core Cmdlet
This feature is a roadmap item as part of the PowerShell Core documentation published on github here. Once this feature is beta or fully released, it will be explained in more detail in this article.
Windows Client Configuration Steps
Client Authentication Option 1) Password-based authentication
- Test the ssh command line by opening PowerShell command prompt (or cmd.exe) as Administrator.
- Run the command but replace your “user-account” and “remotehost”: ssh user-account@remotehost
Client Authentication Option 2) Key-based authentication
Authenticating via SSH is more secure with a key than a password, therefore, these steps are required. To set up a key, you have to generate it from your client and provide a passphrase. The defaults “id_rsa” are used as the file and RSA as the type.
Generating public/private ed25519 key pair.
Enter file in which to save the key (C:Usersuser1.sshid_ed25519):
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in C:Usersuser1.sshid_ed25519.
Your public key has been saved in C:Usersuser1.sshid_ed25519.pub.
The key fingerprint is:
SHA256:OIzc1yE7joL2Bzy8/gS0j8eGK7bYaH1FmF3sDuMeSj8 USER@HOSTNAME
The key's randomart image is:
+--[ED25519 256]--+
| . |
| o |
| . + + . |
| o B * = . |
| o= B S . |
| .=B O o |
| + =+% o |
| *oo.O.E |
|+.o+=o. . |
+----[SHA256]-----+
ssh --% USER@DOMAIN.com powershell -c $ConfirmPreference = 'None'; Repair-AuthorizedKeyPermission 'C:Usersuser1sshauthorized_keys'
Windows Server Configuration Steps of OpenSSH Server (sshd)
- RDP into the Windows Sever as an administrator
- Launch PowerShell command prompt (or cmd.exe) as Administrator
- Verify that PowerShell Core has been installed with the command: $PSVersionTable
- Check that PSEdition says “Core”, with the PSVersion at least 6.0.0.
- Update the Windows Server Enviroment Variables Path:
($env:path).split(“;”)$oldpath = (Get-ItemProperty -Path ‘Registry::HKEY_LOCAL_MACHINESystemCurrentControlSetControlSession ManagerEnvironment’ -Name PATH).path$newpath = “$oldpath;C:Program FilesOpenSSH”Set-ItemProperty -Path ‘Registry::HKEY_LOCAL_MACHINESystemCurrentControlSetControlSession ManagerEnvironment’ -Name PATH -Value $newPath
- Install the OpenSSHUtils as administrator by running: Install-Module -Force OpenSSHUtils
- Ensure the ssh-agent service is started by running: Get-Service ssh-agent
- Check that the status says “Running” otherwise
- Run the command: Start-Service ssh-agent
- Navigate to the OpenSSH folder: “C:Program FilesOpenSSH”
- Run the command: ssh-keygen.exe -A
- The public/private key pair will generate.
- Press Enter to accept the default file name and path of “id_rsa”. Otherwise you can specify a different name and path here.
- Enter a passphrase twice.
- The identification and public key files will be created called “id_rsa” and “id_rsa.pub” with the following output: “C:Program FilesOpenSSHssh-keygen.exe: generating new host keys: ED25519”
- Load the key files into the ssh-agent with the command: ssh-add ssh_host_ed25519_key
- Run the command: Repair-SshdHostKeyPermission -FilePath “C:Program FilesOpenSSHssh_host_ed25519_key”
- Chose “A” as the response.
- Run the command: Start-Service sshd
- Verify the service is in the Running state with the command: Get-Service sshd
- Add the firewall rule that allows traffic on port 22 with the command: New-NetFirewallRule -Name sshd -DisplayName ‘OpenSSH Server (sshd)’ -Service sshd -Enabled True -Direction Inbound -Protocol TCP -Action Allow -Profile Domain
- Go the the OpenSSH directory on the server.
- Open the file “sshd_config” with notepad.exe and add the following to the section “# override default of no subsystems”
Subsystem powershell C:Program FilesPowerShell6.0.0.16pwsh.exe.exe -sshs -NoLogo -NoProfile - Enable password authentication with the text: PasswordAuthentication yes
- Enable key authentication with the text: PubkeyAuthentication yes
- Close and save the sshd_config file.
- Run the command: Restart-Service sshd
PowerShell remoting
PowerShell remoting cmdlets will only allow connection with the command Enter-PSSession, Invoke-Command, etc. It will not work using ssh.exe to connect from the client.
References
- OpenSSH
- Chocolatey OpenSSH
- Powershell OpenSSH
- https://github.com/PowerShell/Win32-OpenSSH/wiki/Install-Win32-OpenSSH
- PSTools
- Powershell make a permanent change to the path environment variable
- Use Powershell to modify your enviromental path
- Powershell Set Service
- How do I open ports with Powershell
- Getting Started with PowerShell Core on Windows, Mac, and Linux
- Microsoft Transitioning Windows PowerShell 6.0 into PowerShell Core
- PowerShell 6.0 Roadmap: CoreCLR, Backwards Compatibility, and More!
- PowerShell Core 6.0: Generally Available (GA) and Supported! –
- PowerShell Remoting Over SSH
- Using the OpenSSH Beta in Windows 10 Fall Creators Update and Windows Server 1709
- Why Remoting vs. SSH Isn’t Even a Thing
- Porting to .NET Core – Libraries (See remoting section)
- Part 2 – Install .NET Core and PowerShell on Linux Using DSC
- Looking Forward: Microsoft Support for Secure Shell (SSH)
Openssh Agent
Share on RedditShare by MailOpenssh Agent Windows
0repliesLeave a Reply
Want to join the discussion?Openssh Agent Windows 10
Feel free to contribute!
Openssh Ssh-agent
Leave a Reply
